
ETHICAL HACKING
Ethical Hacking is the process of breaking into an organization's IT networks and systems to test their weakness and vulnerabilities. There are five phases in hacking. They include reconnaissance, gaining access, enumeration, maintaining access, and covering tracks. Hackers use various hacking tools and techniques in each of these phases. Ethical hackers conduct vulnerability assessment, risk assessment, penetration testing and system protection tests and fix security issues before they are exploited by hackers with malicious intent. A Certified Ethical Hacker is a skilled professional who understands and knows how to look for weaknesses and vulnerabilities in target systems and uses the same knowledge and tools as a malicious hacker, but in a lawful and legitimate manner to assess the security posture of a target system(s).
Basics of Networking and Security: Students learn about fundamental networking concepts, IP addressing, ports, protocols, and the basics of security measures like firewalls and intrusion detection systems.
Introduction to Hacking: Students understand the difference between ethical hacking and malicious hacking, exploring the various types of hackers, hacking phases, and the legal and ethical considerations in hacking.
Information Gathering: This phase covers passive and active information gathering techniques, including open-source intelligence (OSINT), network scanning, and footprinting, to understand the target's online presence and vulnerabilities.
Vulnerability Assessment: Students learn how to identify and assess vulnerabilities in systems and networks using tools like vulnerability scanners and manual techniques, enabling them to understand potential points of exploitation.
Exploitation Techniques: This part delves into various exploitation methods, teaching students about common vulnerabilities like buffer overflows, SQL injection, and more advanced attacks like privilege escalation.
Web Application Hacking: Students learn about the intricacies of web security, covering topics like cross-site scripting (XSS), cross-site request forgery (CSRF), and secure coding practices, preparing them to assess and secure web applications.
Wireless Network Hacking: Students explore the security vulnerabilities in wireless networks, including Wi-Fi encryption protocols, rogue access points, and techniques like WPA/WPA2 cracking.
Network Penetration Testing: In this phase, students learn how to simulate real-world attacks by combining knowledge from previous levels. They conduct comprehensive penetration tests to identify and exploit vulnerabilities in a controlled environment.
Post-Exploitation and Countermeasures: Students delve into the activities that occur after a successful breach, including privilege escalation, lateral movement, and data exfiltration. They also study methods to secure systems and networks effectively, such as implementing patches, intrusion detection, and incident response plans.
Remember that ethical hacking courses should always emphasize the importance of ethical and legal considerations, as well as the necessity of obtaining proper authorization before conducting any hacking activities.

Software Development
₹30,000
JAVA
"Explore the world of Java programming in our comprehensive academy course. Gain hands-on experience in Java syntax, object-oriented concepts, and application development."
Electronic Design Automation
₹25,000
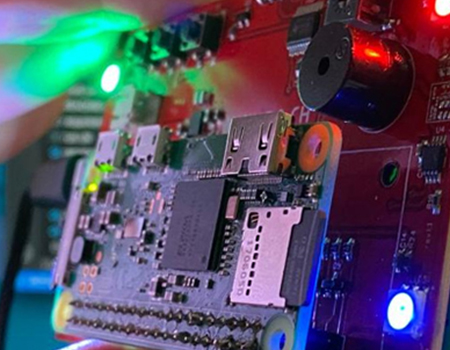
MATLAB for Electronics
"Learn practical electronics using MATLAB in this comprehensive course. Explore circuit analysis, simulations, and hands-on projects for a strong foundation in electronics."

Special Programmes
₹30,000
Data Science
"Unlock the world of data with our comprehensive Data Science course. Learn essential techniques in data analysis, machine learning, and visualization to make informed decisions and drive impactful insights."
Industrial Automation
₹30,000
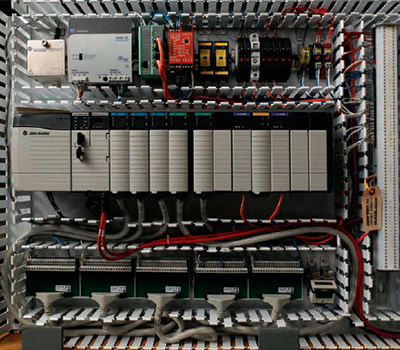
AutoCad Electrical
"Learn to create, edit, and manage electrical control systems using AutoCAD Electrical in this comprehensive course, covering schematic design, panel layout, and PLC integration at our academy. Gain hands-on skills for efficient electrical drafting and documentation."

ITIM
₹30,000
Cloud Computing
"Learn the fundamentals of cloud computing in our comprehensive course: explore virtualization, scalability, and service models while mastering key platforms like AWS and Azure. Gain hands-on experience to deploy and manage applications efficiently in the cloud."

Software Development
₹30,000
Python
"Learn Python programming from the ground up in our academy's comprehensive course. Gain hands-on experience in coding, data manipulation, and building applications."